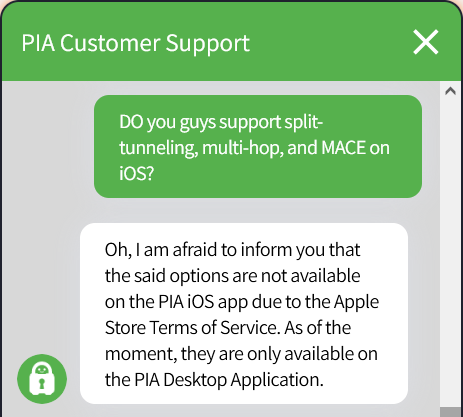
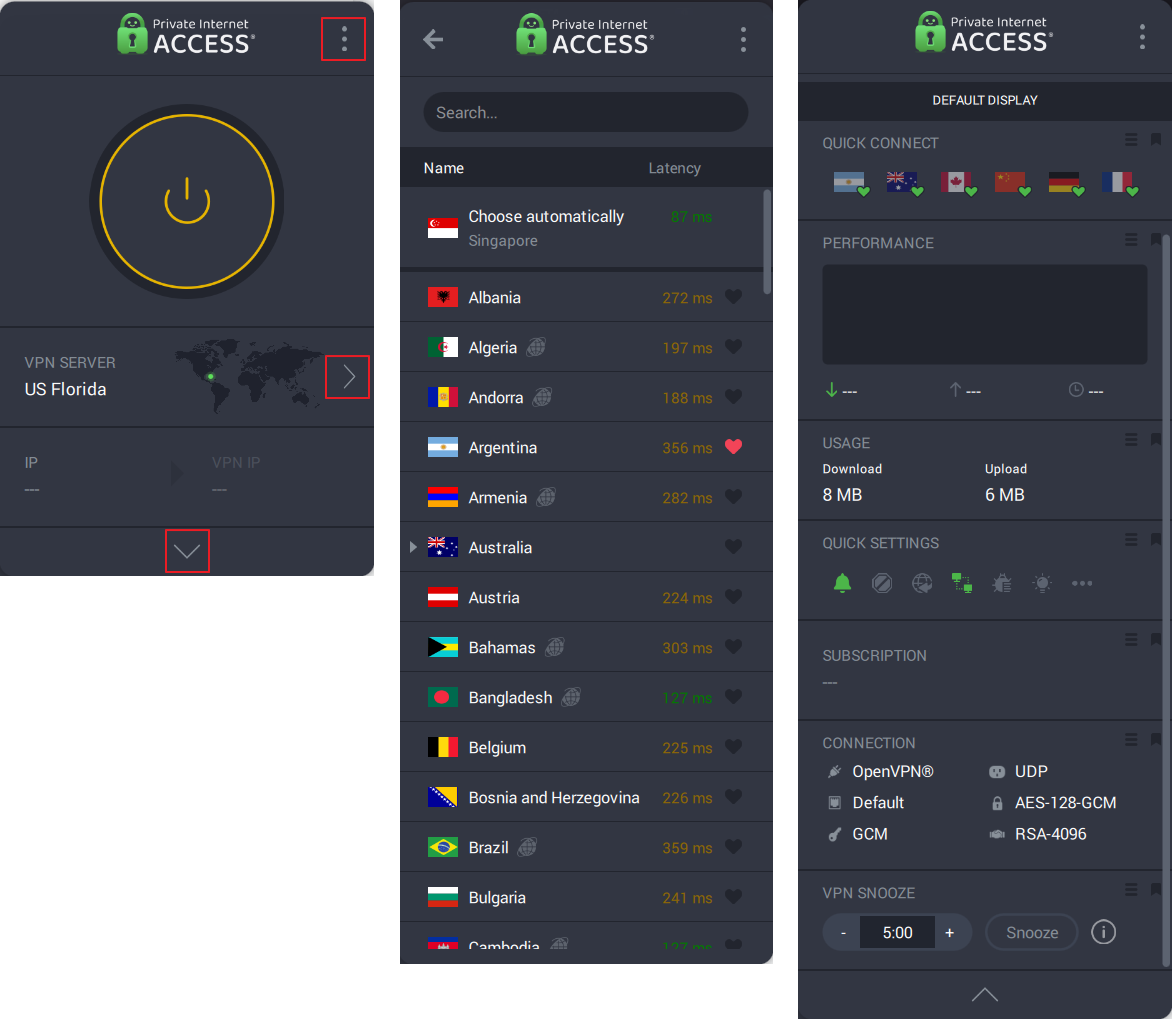
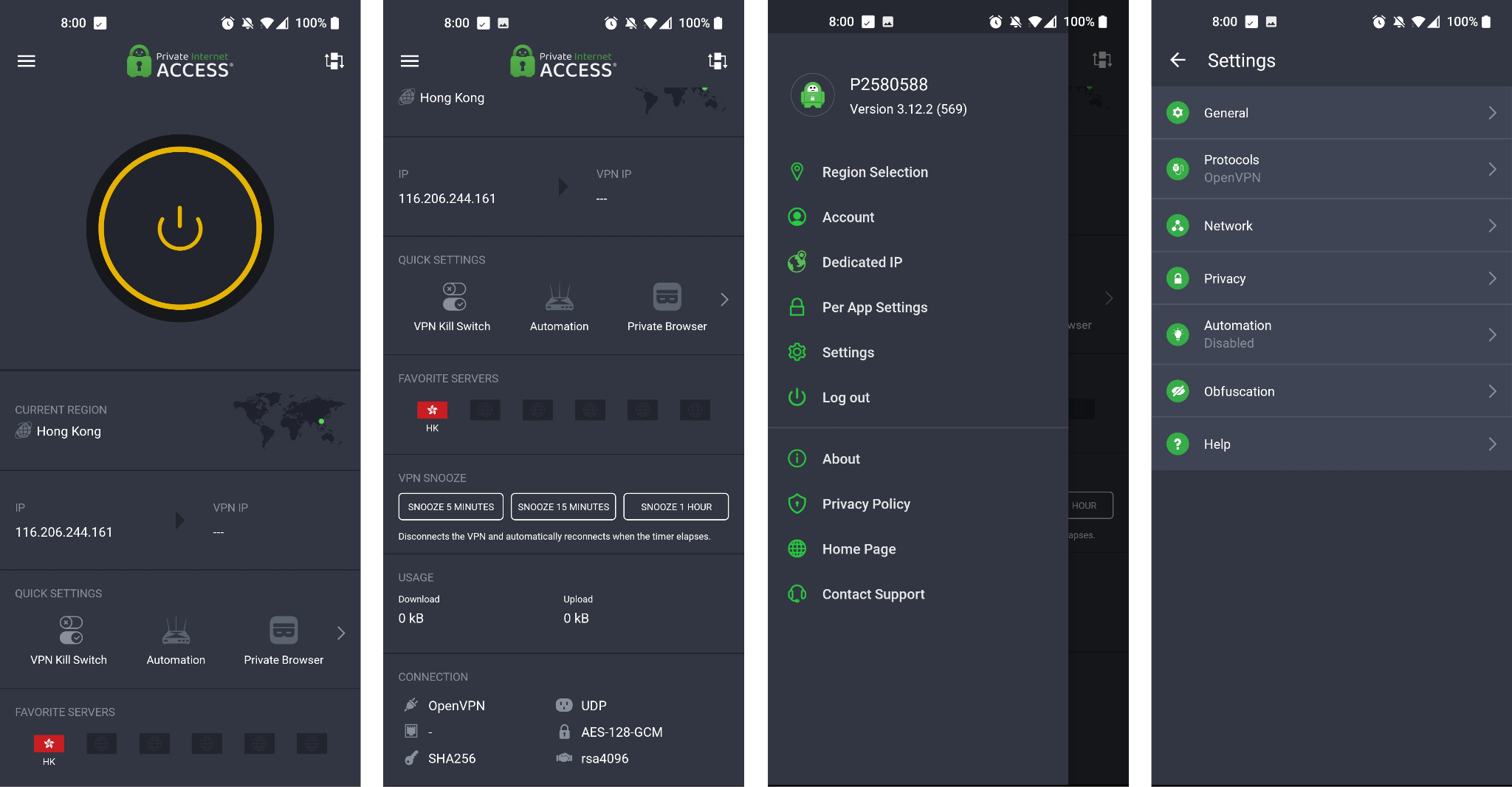
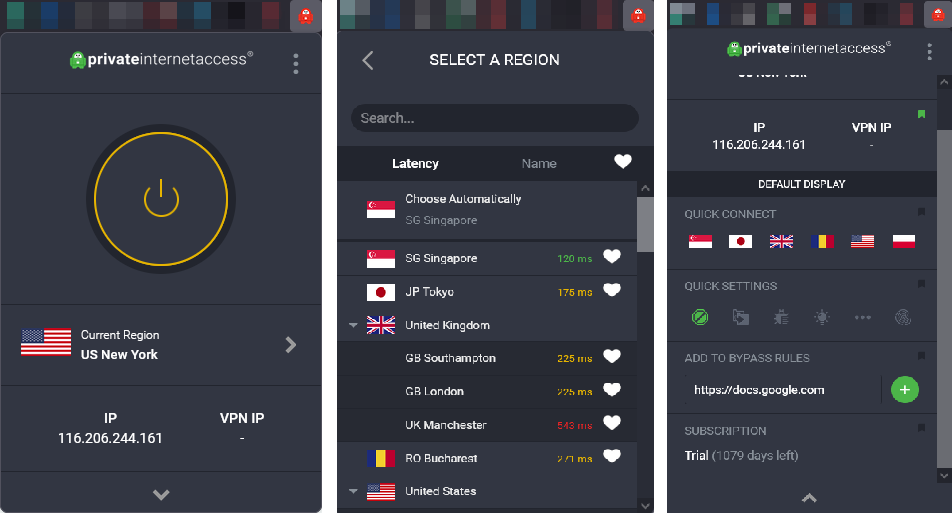
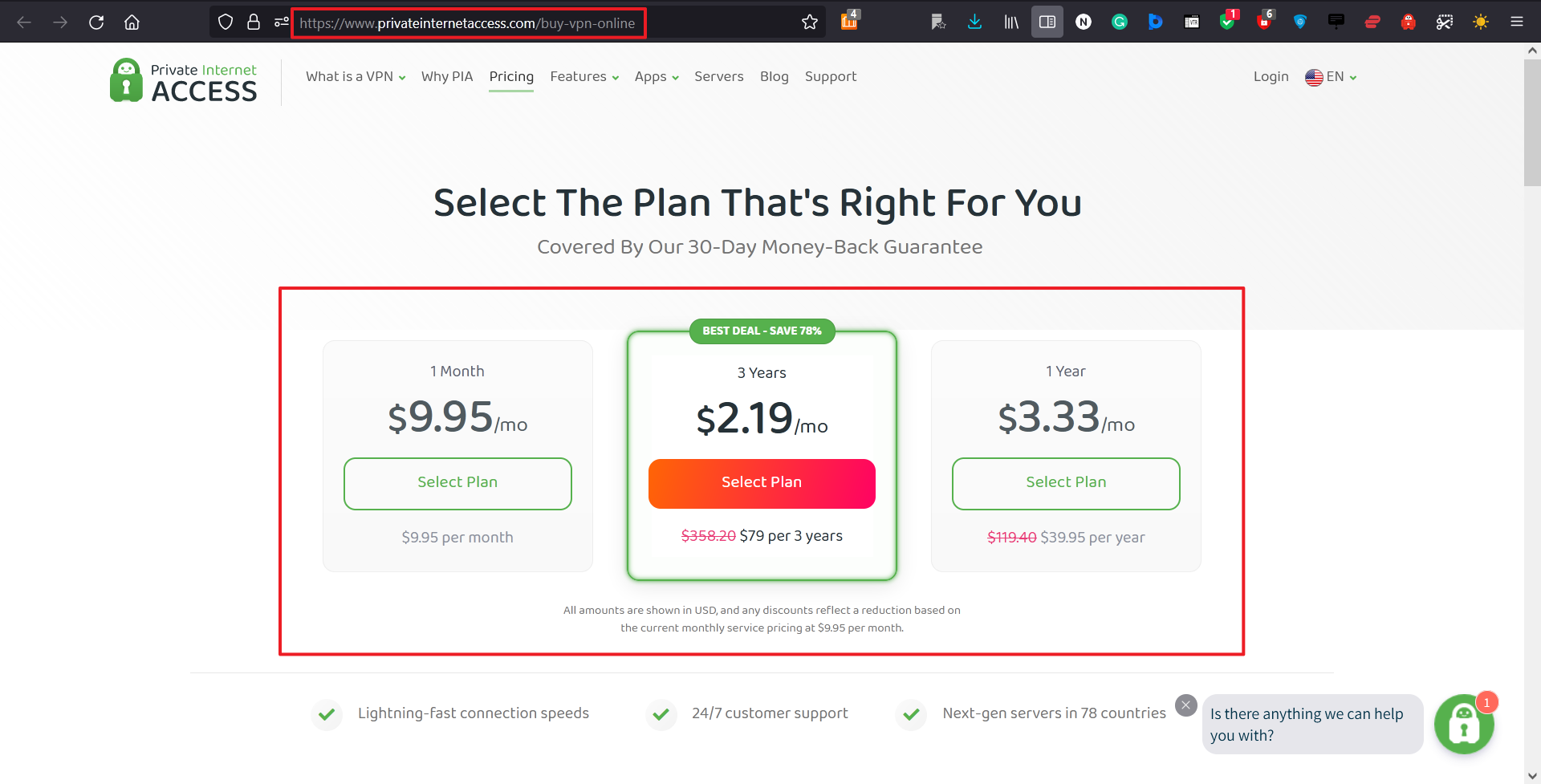
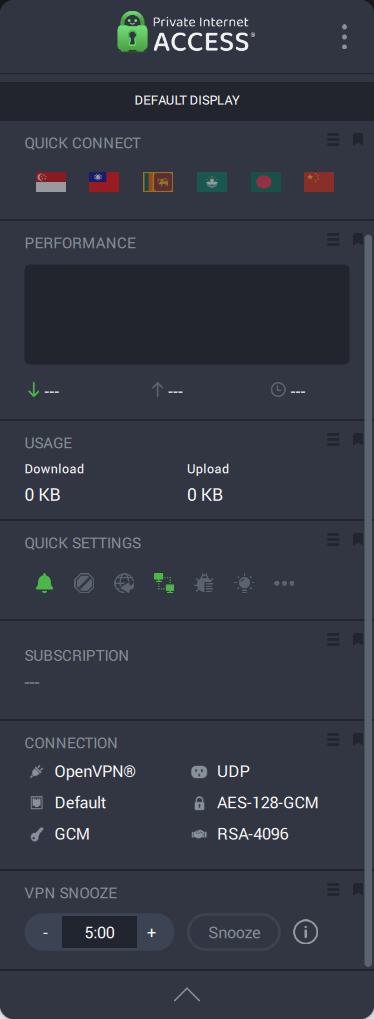
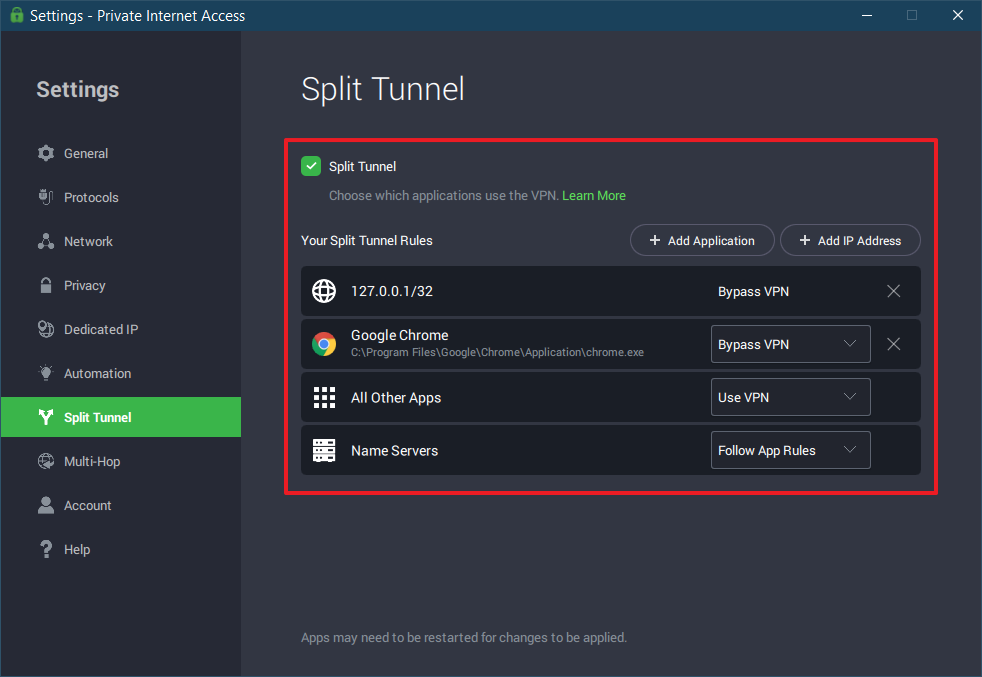
Private Internet Access has a lot of relevant/useful features that legitimately work. It can be useful for small businesses as it allows 10 simultaneous devices and allows for split tunnelling. The upload rates vary in performance so this would be very country-specific. The split tunnelling feature was indeed proven to work as it allows the traffic to a specific IP to go through the ISP, and this was tested using a traceroute command/test. The usability of it is not as great as other VPNs. They do not have a way of bypassing a URL, you need to add an IPV4/IPV6 address or a subnet in CIDR notation, which may not be very user friendly for some people. The applications are easier to bypass, however.
They also have a ‘PIA Mace’ feature to block adverts and malware. This option worked well to block pop-ups, requests for notifications and adverts on a variety of websites.
The VPN experienced no DNS leaks or DNS intercepts. For the various leak tests undertaken PIA never disclosed that a VPN was being used. Even with a whitelist in place for split tunnelling, the anonymity was never compromised when on other sites. Websites that warn you to use a VPN also did not detect any information that reflected my actual ISP and IP address etc.
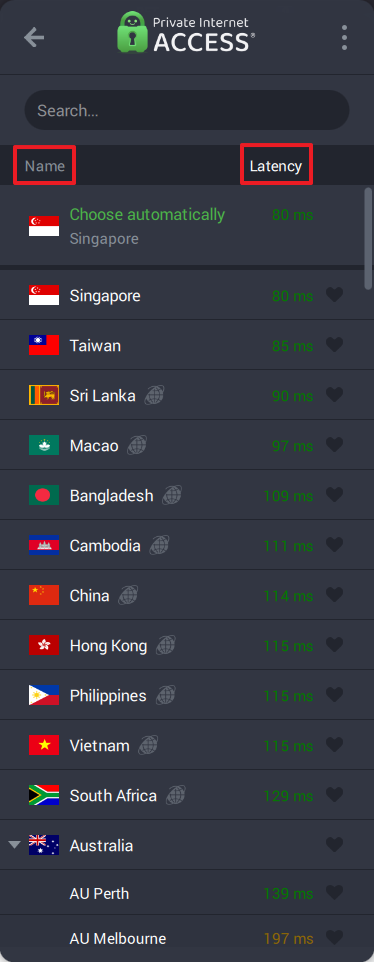
The provider also claims to use strictly bare metal servers with some acting as exit nodes and others as proxy servers. They are transparent about which servers are geo-located and which ones are physically in the locations stipulated. However, the South African servers are supposedly not geo-located, but the results of the speed test do not reflect this. The latency on the speed test for the local server was 569ms, and it should have been less than 10ms if it was indeed in the same country.
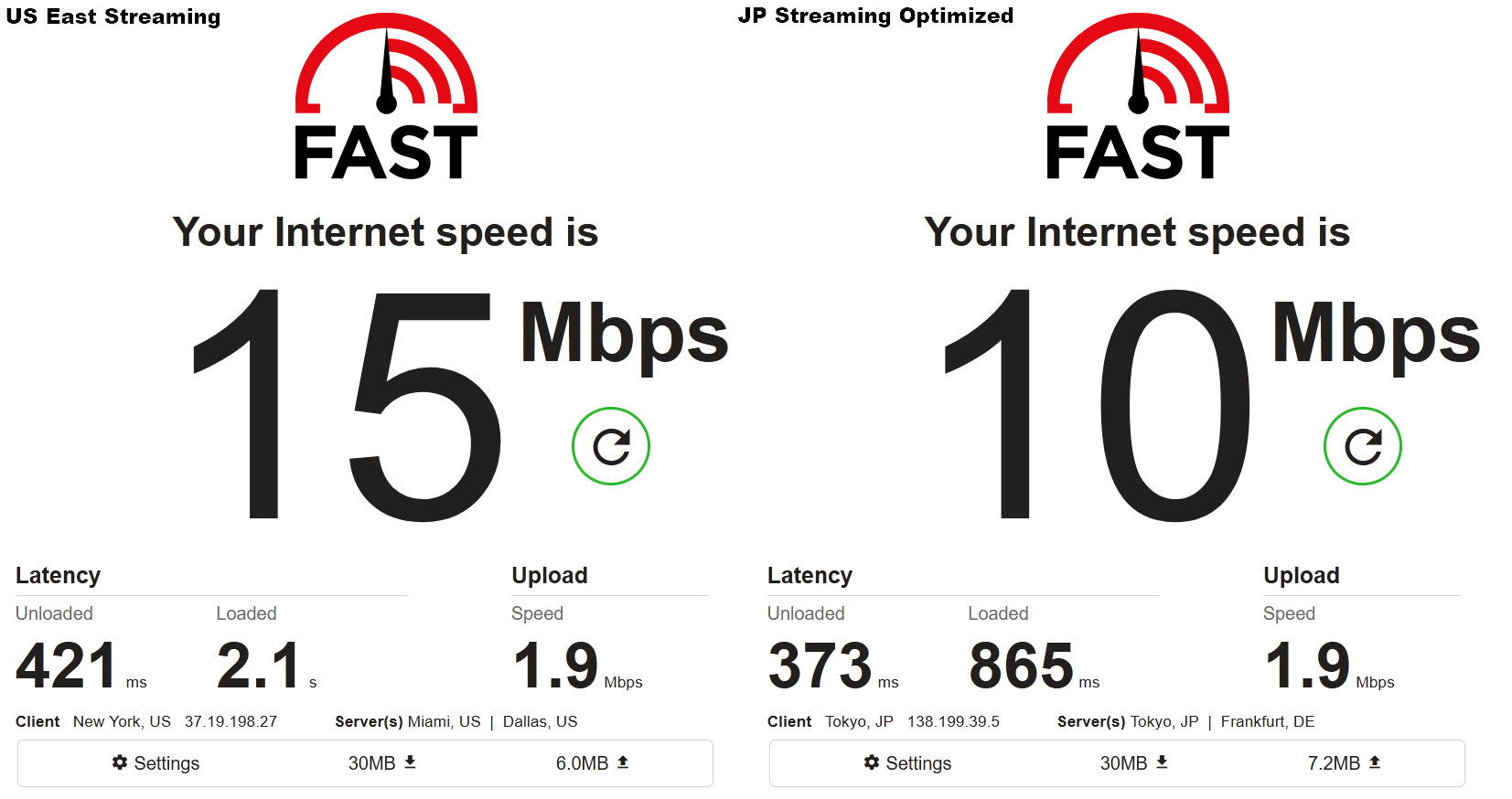
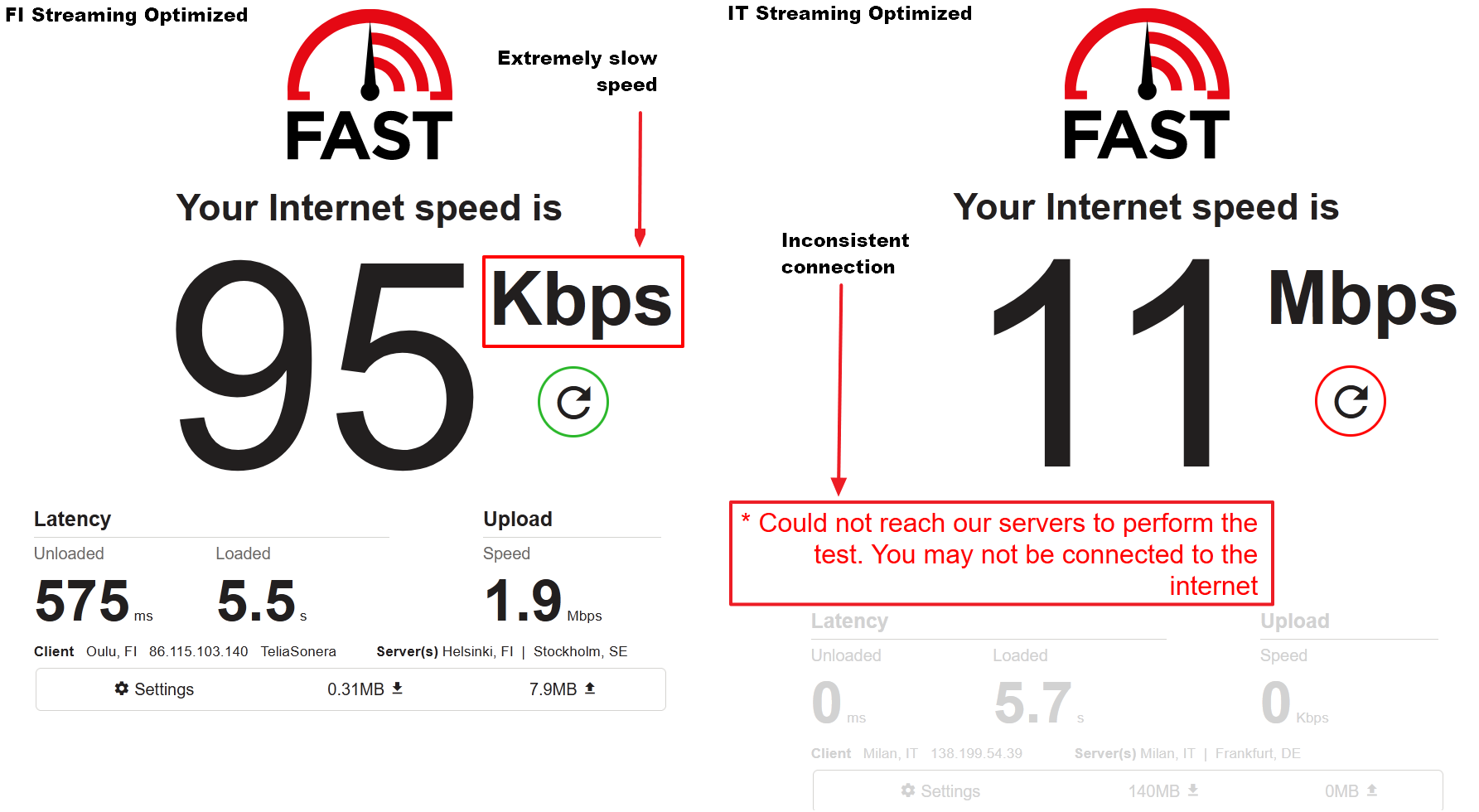
Regarding speed, the average drop was more than 60% for download rates. This is a significant overall drop thus the performance isn’t high ranking amongst other previously tested VPNs. The largest drop being 76% (ironically enough for the South African Server) and the smallest drop being 25% (Toronto, Canada). Regarding Upload rates, the drops varied between 25-75%. The largest drop being 89% (Mumbai, India) and the smallest drop being 16% (Berlin, Germany). Six of the servers had a latency of less than 200ms when speed tested between it and an optimal server. This is good news for users that perform applications that need low latency to participate.
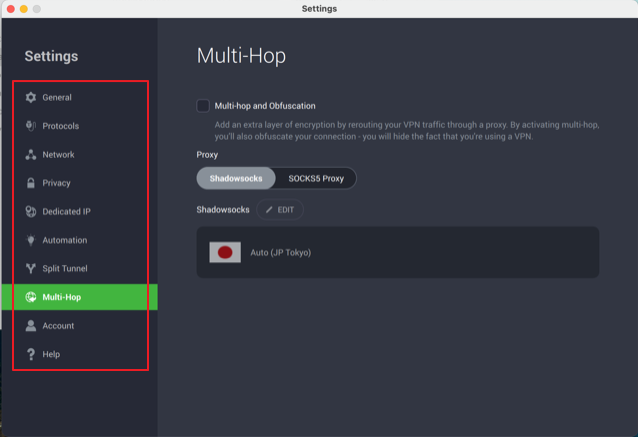
There is a multi-hop and obfuscation server functionality that allows you to select your proxy server of choice. Each combination of the primary server and proxy server produced different performance results. The extra layer of encryption would often quadruple the latency and half or quarter the upload/download rates. The several combinations tested did unanimously lessen the overall performance. The user will have to find their ideal combination, but the speed will unlikely ever be as good as the exit node alone without the proxy server involved.
The VPN is completely open-source and also makes use of open-source protocols. This can lead to improved security and innovation which can improve it vastly in the years to come. However, some users may prefer a very well-performing VPN over one that is mediocre but also open source.
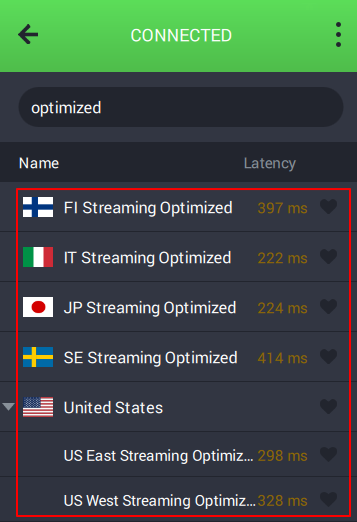
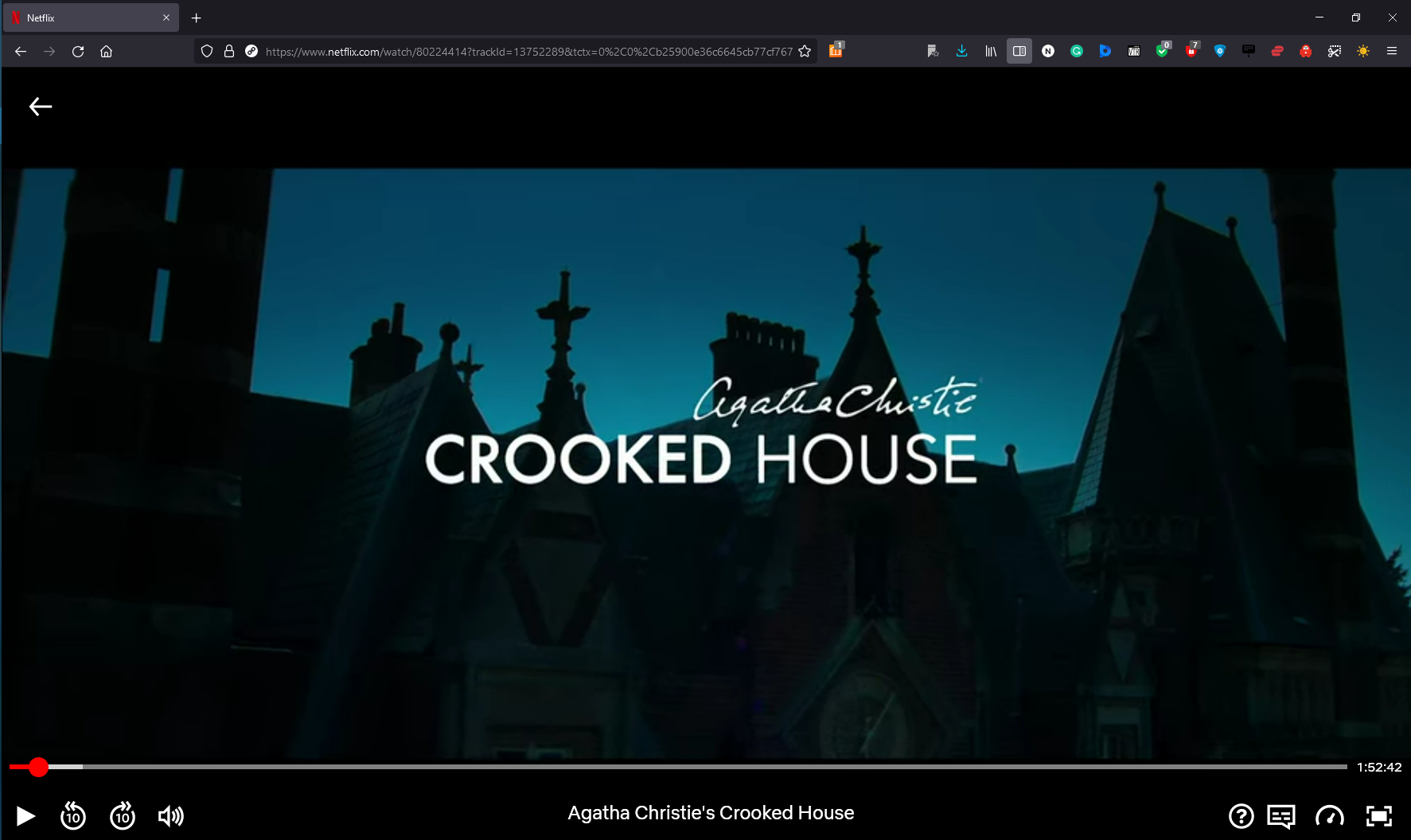
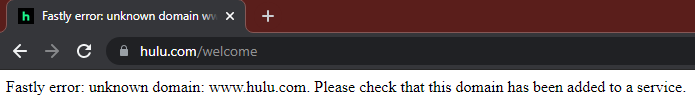
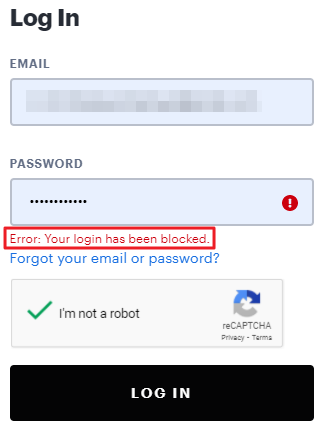
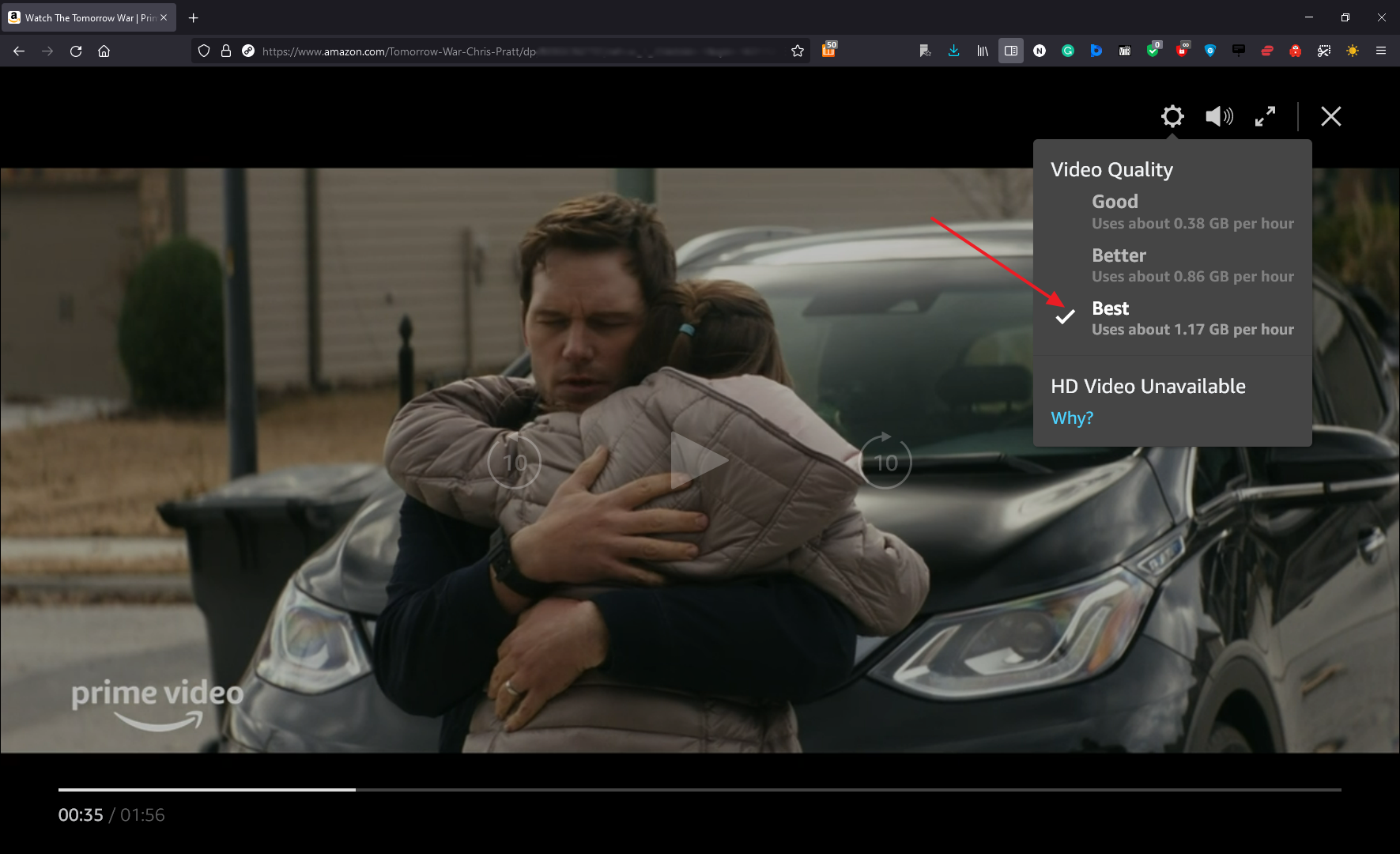
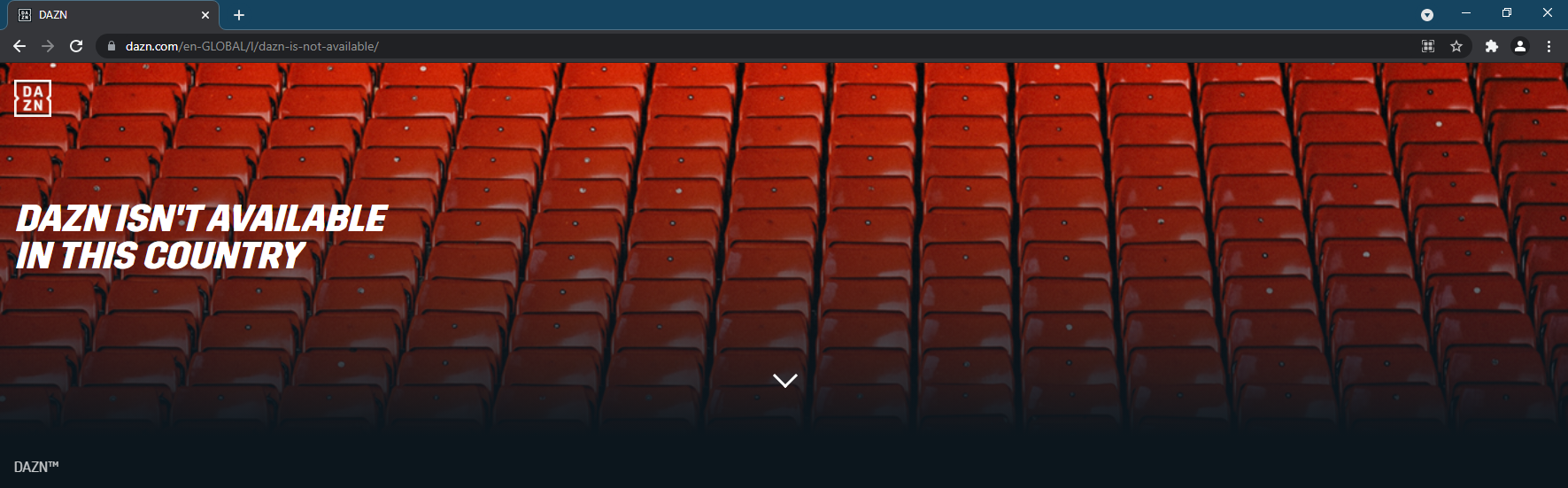
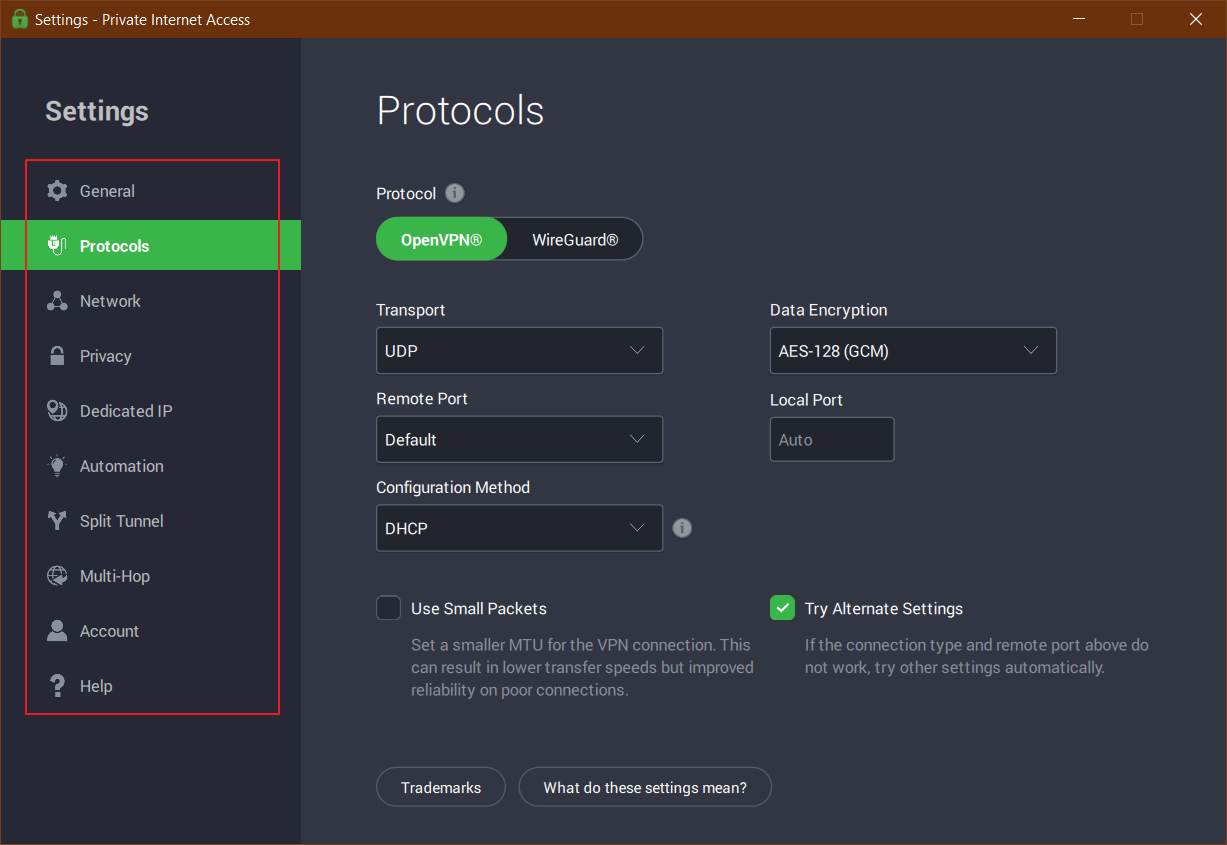
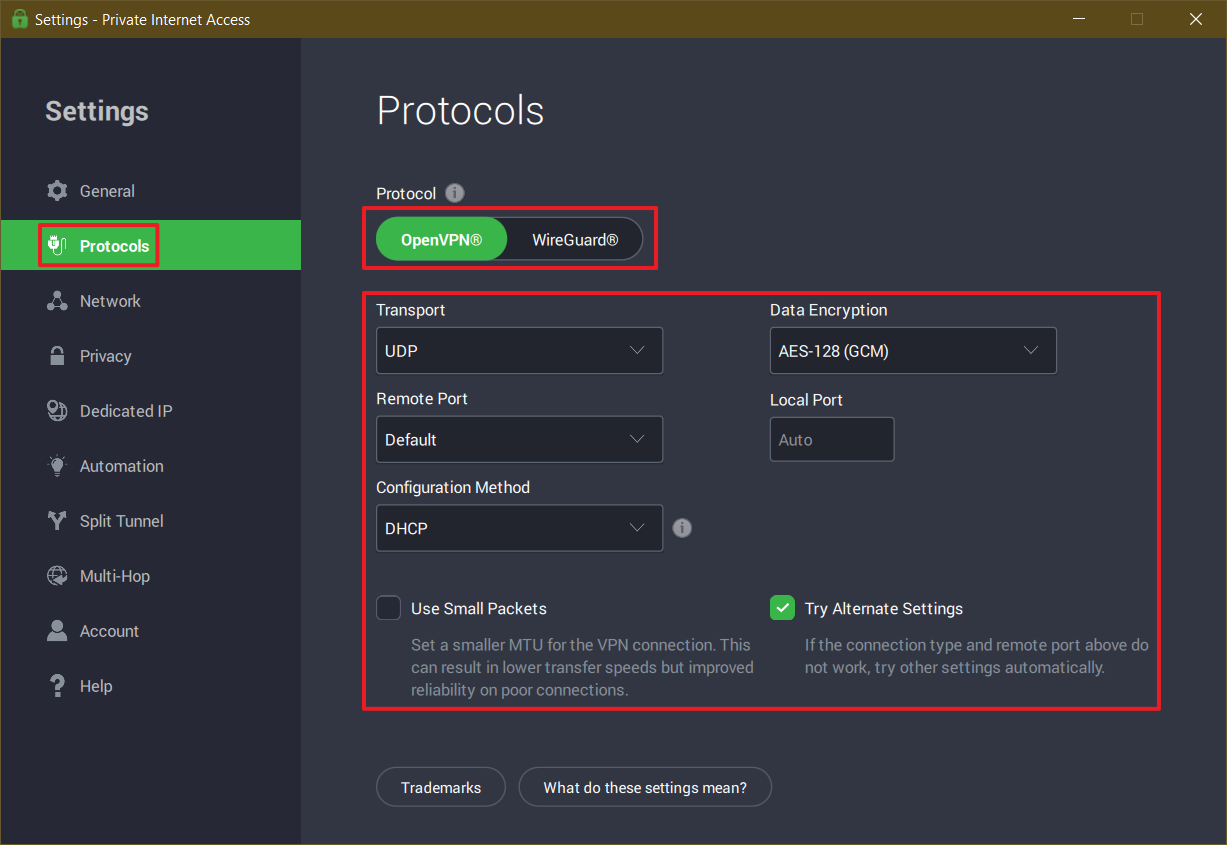
Some functionality requires that you use a specific protocol. However, for performance, WireGuard fared better than OpenVPN. All tests conducted used WireGuard. The designated streaming servers fared well in terms of streaming YouTube/Netflix even in the highest quality available on each platform. They also unblocked geo-restricted streaming websites very easily. However, the provider has removed their assets from Russia and South Korea due to them being seized in the past.
Overall the performance is satisfactory, but this set-up may not be for the complete VPN novice.