Technological advancements have changed the world for the better, but there are also some adverse effects. Cyber security is one. You must be familiar with words like data breach and data leak. To tackle these breaches, you will be introduced to an open-source torrent client: qBittorrent.
In comparison to other torrent clients, qBittorrent has a tonne more features. However, you'll notice the same privacy breaches that might jeopardize the entirety of your torrenting history. With this complete guide, you can take care of these security issues.
To use qBittorrent with a VPN, proxy, or both, you must first download a reliable VPN, SOCKS5 proxy, or both, configure the VPN, and then connect to a P2P (peer-to-peer)-friendly VPN server. Establish a proxy and check your connection. Using qBittorrent, you may now download torrents without risk.

Simply download a trustworthy VPN service, sit back and let it handle everything. While not all VPN services are equal, keep in mind that some are not even geared for torrenting.
A server on the internet that has opened the necessary ports for torrenting. Connecting to a proxy server will let you use its IP address to access the internet. Its the underlying technology of VPNs.
NordVPN is the most famous and highly reviewed qbittorrent VPN server. It offers several P2P-ready servers, one of the market's most robust (and most inspected) no-logging policies, and unmatched privacy safeguards.
Along with the military-grade AES-256 encryption, you also receive a wide selection of Double VPN servers that let you reroute your internet traffic across several VPN servers to almost eliminate your ability to be tracked.
Furthermore, NordVPN takes pride in its WireGuard VPN technology, which enables you to keep a high privacy profile while still getting lightning-fast download speeds.
Although not all NordVPN servers are P2P-friendly, they are most reliable and consistently provide reasonable torrenting speeds.
NordVPN comes with a 30-day, no-questions-asked money-back guarantee.
Read our detailed review of this solid VPN service: NordVPN Review
Pros:
Cons:
Surfshark made its debut in 2018 with the release of its first VPN app for iOS devices. The German cybersecurity company Cure53 conducted a 2018 external audit of Surfshark, but just for its browser extensions. In 65 countries, Surfshark has more than 3,200 servers.
In September of this year, Surfshark published the Android app Trust DNS. The program functions as a DNS resolver that can grant access to websites in countries with many restrictions. Surfshark was one of the first ten VPN providers to receive formal clearance from the independent IT-Security Institute AV-TEST in October 2019. CNN recognised Surfshark as the top VPN of 2020.
Surfshark introduced GPS-Spoofing for Android in December 2019, enabling users to conceal their device's actual geo-location by setting it to one of the server locations. Surfshark employs the IKEv2, OpenVPN, and WireGuard tunneling protocols in its apps. All information transported through Surfshark servers is secured using the AES-256-GCM standard.
Surfshark Review by Industry Experts
Pros:
Cons:
Atlas VPN is a terrific all-around gaming VPN with more than 750 highly-optimized servers that can give impressive speeds and minimize lag. It is effortless to set up and combines heavy-duty security features with the ease of quick access.
The best-in-class WireGuard protocol is included in Atlas VPN apps to provide seamless and secure gaming. Private DNS, split tunneling, a kill switch, and a few special features like SafeSwap and MultiHop+ are also included.
However, there is more. A fantastic free VPN subscription with a smaller number of servers is also available from Atlas VPN. This can be an excellent alternative if you don't have the extra cash to spend on a VPN subscription.
Pros:
Cons:
Another excellent VPN for Roobet is ExpressVPN. With servers in over 90 countries, it offers a VPN with a strong focus on privacy. ExpressVPN does not save any logs on their servers since they all run on RAM disk.
This VPN has a Network Lock and uses industry-standard AES-256 encryption. It features secure OpenVPN, IKEv2/IPSec, and L2TP/IPSec protocols in addition to IP and DNS leak protection.
ExpressVPN takes advantage of remote virtual servers. This enables you to retrieve a connection with an IP address associated with the location you prefer, while the VPN actually establishes a connection to a server physically situated in another area that can offer faster internet.
Websites that are blocked can easily be unblocked with ExpressVPN – even in nations like Iran, the UAE, and China. Using a premium VPN like ExpressVPN, you may access Roobet from anywhere.
Pros of ExpressVPN:
Cons of ExpressVPN:
The low cost of Private Internet Access membership is well known. Most likely, PIA is the only service that provides the same functionality at the exact price. Although the UI isn't as pristine as some of its rivals, we're focusing on the overall value here.
First of all, unlike many VPNs, PIA offers port forwarding functionality. It may be an effective instrument that you employ. If you're new to VPNs, we do not advise experimenting with port forwarding since you may encounter security problems that you are unaware of.
You may set up public services such as web servers, FTP servers, email servers, and other specialised Internet programmes on your network by using port forwarding. Port forwarding is of two types: Single port and Port range forwarding.
This USA-based qbittorrent VPN(used with qbittorrent) has a comprehensive set of privacy protections and strictly adheres to no-logging regulations.
Pros of PIA:
Cons of PIA:


Although using a VPN is not necessary for the second method, I strongly advise doing so to get the best outcomes.
The most important tip is never to utilize a free proxy service you might find online. This is due to several factors, including:
They'll continue to retain logs and record your torrenting activity.
They may not function at all.
They are often quite sluggish.
Typically, they disable torrent ports until you sign up for a premium service.
To generate income, they may employ obtrusive marketing strategies.
They can introduce malware to compromise your systems.
SOCKS proxies don't provide the same level of encryption as VPNs may be both a blessing and a problem. Although unencrypted data can be intercepted and recorded, unencrypted data frequently offer much faster download rates.
You should know that utilising a SOCKS proxy within a torrent client won't alter your browser's real IP address. Your torrenting behavior will be the only thing it conceals.
Finally, using proxy servers, magnet links could not function properly. You must download the.torrent file to your PC and open it using qBittorrent for unknown reasons.
The highest level of protection is achieved by installing a VPN service and utilizing a SOCKS5 proxy simultaneously.
Imagine that qBittorrent downloads the files using a different, unique IP address from your web browser, making it nearly impossible to track your online behaviour.
Doing this allows you to browse torrent websites and download torrents without knowing your ISP. Your whole identity will be hidden, and your activities will be highly encrypted.
This is not required, even though it might seem like the optimal method to utilise qBittorrent. Your additional layer of safety should be provided by a VPN, which should be more than adequate.
It won't harm to enable both options if you value your privacy.



The simplest solution to keep your torrenting secret is definitely to use qBittorrent together with a VPN. The only steps required are to sign up for a non-logging VPN service, download the VPN, and connect to a P2P-friendly VPN server.
However, there are two things to remember. The kill switch feature of your VPN is the first since it detects any changes in network traffic and promptly halts all of your online activities.
When a VPN server crashes, your real IP address will be public if the kill switch option is not activated.
The second is DNS leak protection and IPv6. They can still get your IP address if concealed, but your DNS is publicized. Verify that both settings, i.e., DNS Leak protection and IPv6 are active on your VPN.
You must be informed that even though you will be torrenting using a separate IP address and an unencrypted connection before configuring your client. Thus, your ISP can still identify that you are torrenting and limit your download speeds.
Please refrain from using HTTP(s) proxies. Simply ignoring the proxy server will allow your qBittorrent client to display your actual IP address.
Navigate to Tools -> Options -> Connection in your open qBittorrent client. You may immediately access the options menu by pressing “Alt+O.”
Under the connection tab, you'll discover the Listening Port, Connections Limits, and Proxy Server. The Connection Limits tab won't alter at all.
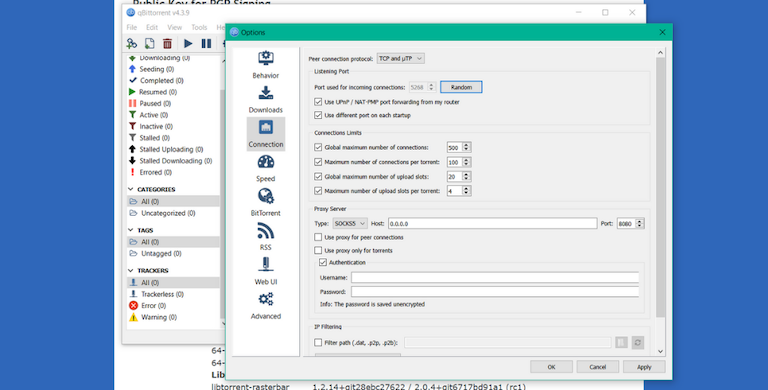
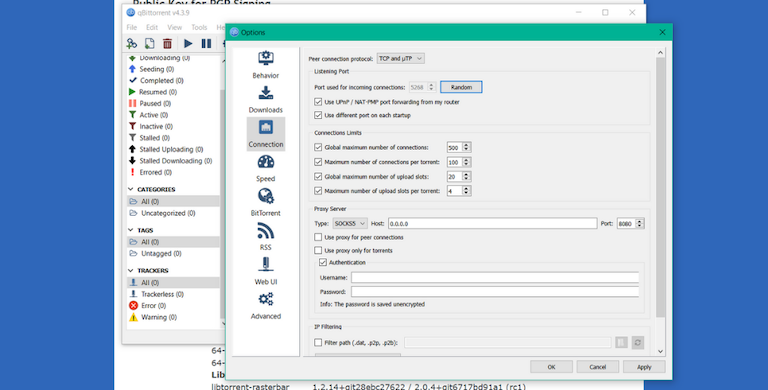
Your client will hunt for new peer connections on the Listening Port. The “Port Number for Incoming Connections” must first be established. You may select any random port or generate one by pressing the “random” button.
Next, select “Use UPnP/NAT PMP” from the list of options. Your customer will be able to automatically forward the given port through your router thanks to this.
The final option is “Use a Different Port on Each Startup.” To maintain maximum privacy, keep that checkbox selected. Turn it off if you experience problems when torrenting.
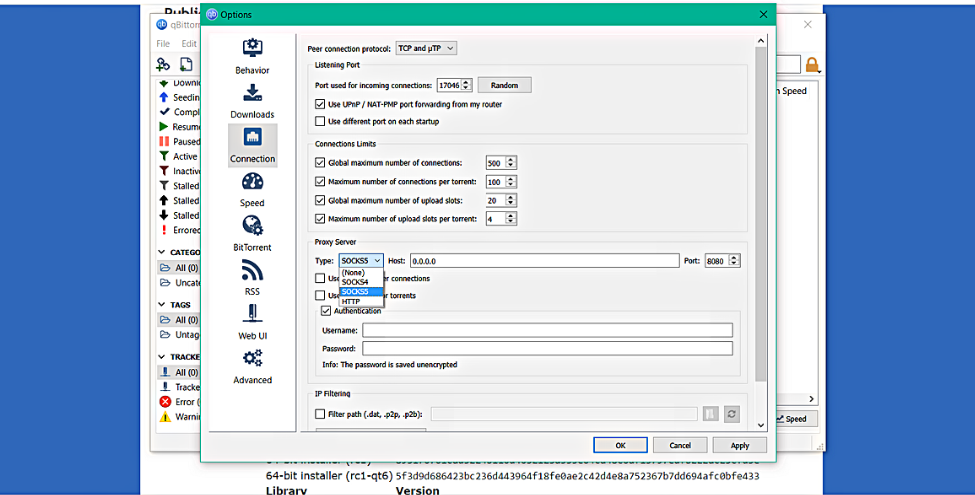
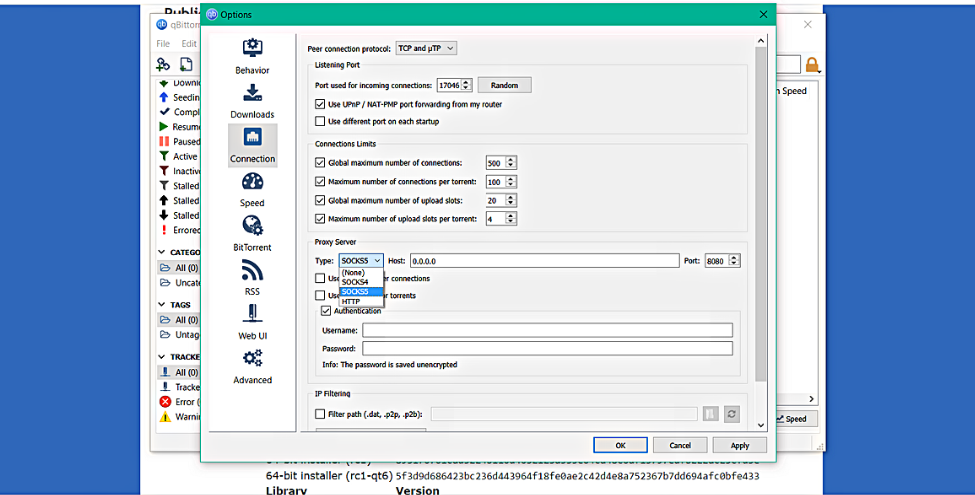
Now is the time to set up the proxy server, which is the most crucial stage.
The credentials of the VPN provider you choose must be verified here. Although each VPN's credentials and port numbers vary, they are easy to locate. Either the website's forum or your VPN program will include a list.
The host address and port number are the initial items under Proxy Settings. You will then see a checkbox labeled “Authentication.” Verify the username and password provided by your VPN for setting up the proxy server.
Enter the username and password that your VPN programme assigned to you. Once you've completed, your torrent downloads will no longer happen using your actual IP address.
Please be aware that NAT port mapping or UPnP are often activated on routers. You must also configure your router's port forwarding settings if neither is enabled. It will still work if you don't, but you won't be able to build any good peer connections.
You will gain the following three key benefits from utilising both a proxy service and a VPN:
One IP address is for qBittorrent, while the other is for your browser.
Both of these IP addresses are different from the one you have.
Your browser activity will be encrypted to prevent the ISP from discovering that you are downloading torrents.
You can have perfect network privacy by combining the two approaches. It's not essential if your ISP doesn't have a reputation for slowing down torrenting speeds.
If you've decided to combine both services, check for VPN providers that provide a proxy service at no additional cost. All the VPN services we recommended are reasonably priced and offer a free proxy service.
However, you must complete the procedures listed below in sequence before you may begin torrenting.
To begin with, make sure the qBittorrent client is shut down and not active in the background. This is crucial because using the specified proxy while qBittorrent runs will result in a proxy server error. When the IP address changes, the proxy server reports this error.
Next, activate your VPN and join the remote server. You may now launch qBittorrent without any issues after your VPN is connected.
Checking your IP address is the most straightforward approach to see if your VPN is operating correctly. If it differs from your actual one, it is functioning flawlessly.
The use of a proxy server will prevent this from working, though. Nevertheless, you may still use the following techniques to confirm that your IP is concealed.
You receive a magnet link from ipMagnet that contains a fake torrent download. As soon as this torrent begins downloading on your qBittorrent application, you should be able to see the IP address downloading the file on the same webpage.
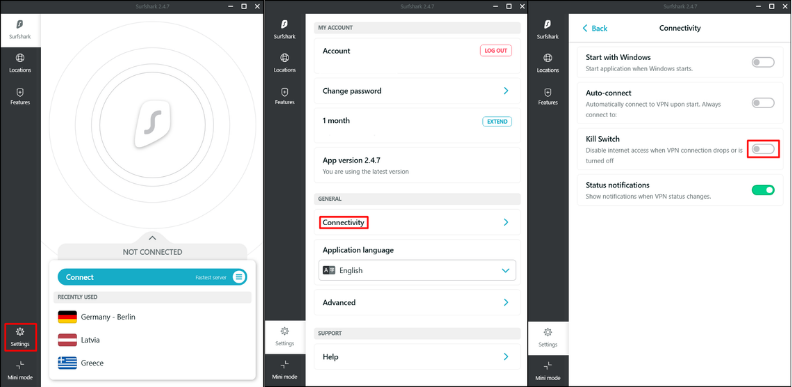
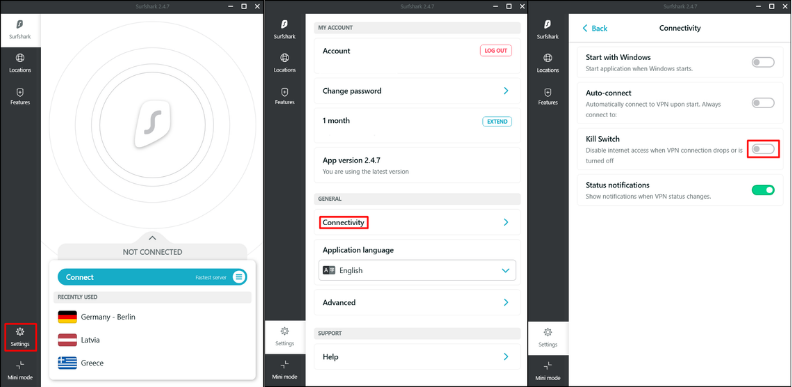
Almost all VPNs feature a kill switch.
VPNs provide a kill switch function in addition to various other privacy features.
You can quickly test your VPN's kill switch because some VPN companies promote capabilities that they either don't have or don't function properly. You must first connect to your VPN, launch your qBittorrent client, wait until the download has begun, and then disconnect from the VPN.
Your kill switch is ineffective if your qBittorrent client doesn't instantly stop downloading torrents.
You are undoubtedly already aware that qBittorrent, like all other torrent client, does not encrypt your communication and does not mask your IP address.
There is another significant reason why VPNs are necessary while torrenting, in addition to helping you secure your privacy and, in the case of NordVPN, providing more excellent encryption.
When you pirate, your ISP generally doesn't appreciate it, especially if you have an unlimited data plan. Your ISP can identify your torrent downloads and limit your speeds since your downloads aren't adequately encrypted.
Of course, other businesses can also keep an eye on your traffic rather than your ISP; they may do so for various reasons. Others could even turn it against you!
Even worse, one website exposes your whole torrenting history to the public and uses the same surveillance methods.
Given that it is clear why using a VPN to conceal your torrenting activity is necessary, let's now discuss how to utilise qBittorrent securely and privately
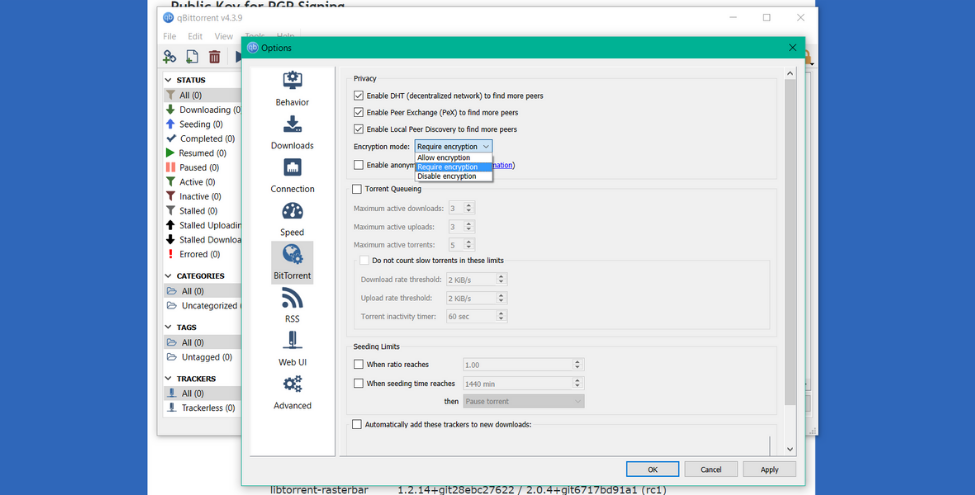
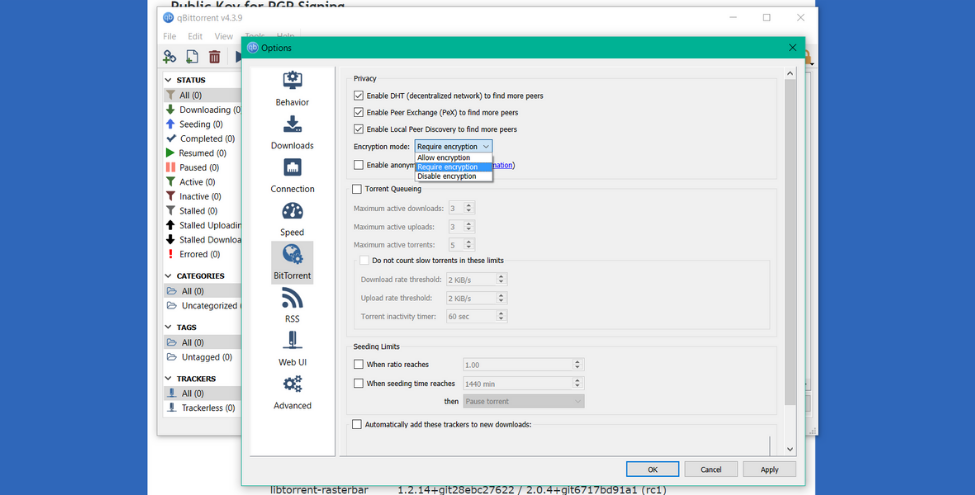
If you're thinking of forgoing a VPN and utilising qBittorrent's in-built encryption, you should be aware that this isn't the best option.
There are many reasons why doing this is a bad idea. The first reason is that your IP address will still be made public. The second difference is that most VPNs employ military-grade AES 256-bit encryption, whereas qBittorrent's encryption uses RC4.
This encryption can stop your ISP from slowing down your connection, but it is not as secure as AES encryption. The fact that RC4 encryption would materially slow down your download speed is why you shouldn't use it.
This occurs because RC4 encryption lowers the number of accessible speeds (peer availability), which can dramatically slow down your download rates.
The ideal response is still to use VPN software. However, if you use an RC4-encrypted proxy server for the qBittorrent client, you may still enjoy a reasonable level of anonymity.
Yes, it is the solution. This functionality, which acts as an extra kill switch functionality built into your vpn interface, comes highly recommended.
Yes, you may pick a VPN provider with a kill-switch option, but it only adds another layer of security and requires a little setup time.
The concept is that once you begin utilising a VPN service, it will build a virtual network adapter of its own to carry out traffic routing. You can quickly examine your active network adapter from Control Panel -> Network & Internet -> Network Connections.
“Bind to Network Interface” is a functionality of qBittorrent. The client is compelled to use just the chosen network adaptor. Your client won't have peer connections to download or upload anything if your active internet connection is something other than the VPN's network adapter.
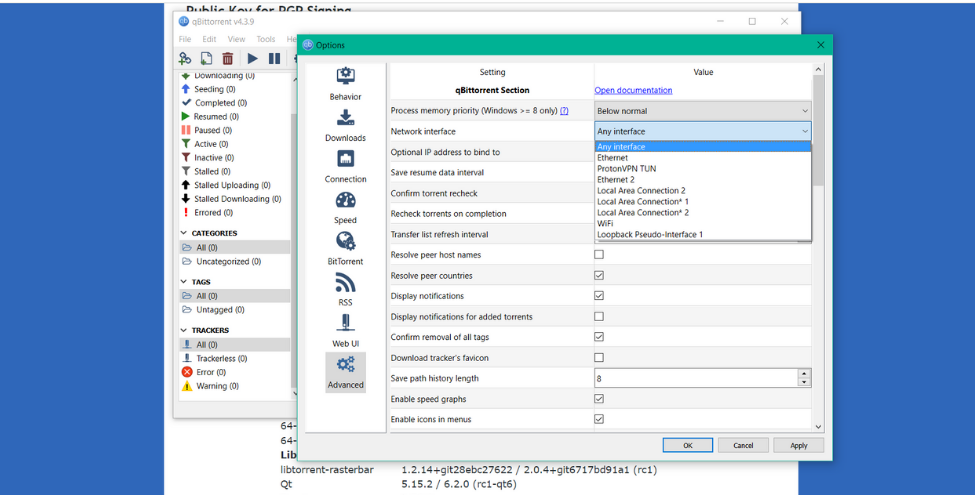
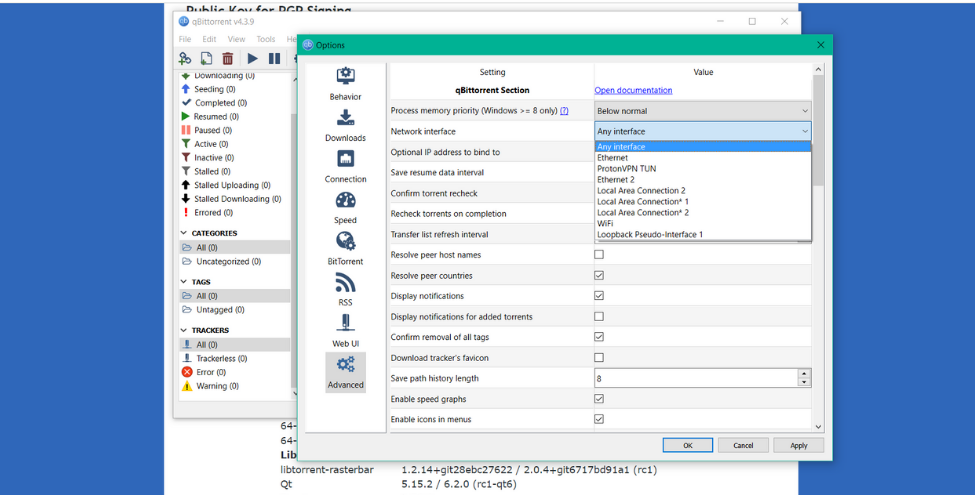
Make sure your VPN service is operational first. Next, check your Network Connections to see which network interface is active.
By visiting its characteristics and checking the time it has been active, you can readily identify it as your VPN adapter since all other adapter networks should be dormant (greyed out).
The next step is to navigate to Menu -> Tools -> Options -> Advanced in our qBittorrent client. A chosen network adapter is next to the option labeled Network Interface (requires restart). After choosing the VPN network adapter, restart your client.
“Anonymous Mode” is another another cool qBittorrent feature. Although this function can provide a layer of protection, it cannot be used to its full potential without a VPN or proxy service.
The purpose of “Anonymous Mode” is to hide some inconsequential information that may be exploited to reveal your data. Among them is preventing all peers and trackers from seeing your metadata and other identifiable information.
As soon as “Anonymous Mode” is activated, it will:
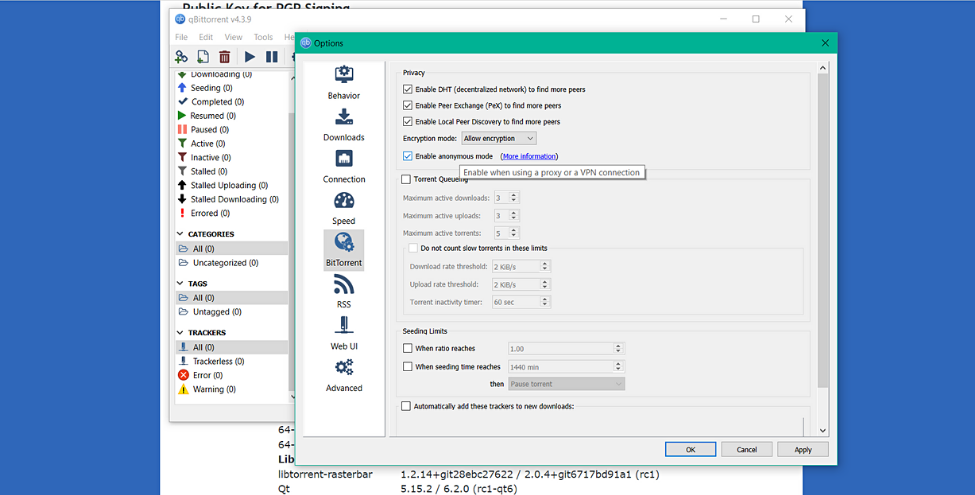
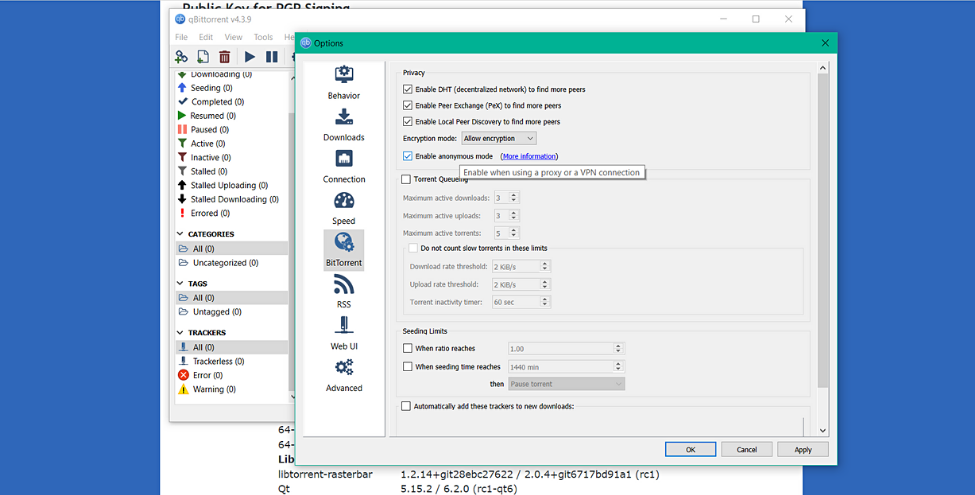
The first action is to select BitTorrent under Tools -> Options. You may choose to “Enable Anonymous Mode” from that menu.
Don't rely only on this function to conceal your data; remember that qBittorrent classifies it as “Experimental.” Without a VPN and this functionality activated, your peers can still see your real IP address, putting your data in danger.
Please be aware that utilising IP filtering without a VPN is essentially worthless before continuing. Your activity logs are still being kept, your IP is still observable, and your data can still be tracked.
With qBittorrent's IP filtering tool, you may import peers or trackers known to engage in criminal activity and completely ban them.
IP filtering has two applications. The first is entering the IP addresses you want to ban manually in settings. The second involves visiting an outside website containing a sizable blocklist collection and adding the IP addresses to qBittorrent.
If you attentively followed our instructions, you now understand how to utilise qBittorrent in the most confidential manner possible. The most crucial step is to sign up for a reputable and well-known VPN. If you don't succeed in the first phase, your torrent files downloads may draw unwelcome attention to you and put you at risk for copyright lawsuits.
Here are our responses to the most asked questions in regards to qBittorrent VPNs:
1. Is running qBittorrent safe without a VPN?
No, it is not. Although qBittorrent offers several fundamental security features, they are insufficient to hide your IP address.
2. Why does qBittorrent not start downloading with VPN?
It's possible that qBittorrent or your VPN is not configured correctly. Think about turning on IP binding and port forwarding, or try switching the VPN server.
3. What is the best VPN for qBittorrent?
We recommend NordVPN, Surfshark, ExpressVPN, PIA, and AtlasVPN as the best clients that work with qBittorrent.
4. Is IP binding a better option than split tunneling for qBittorrent?
On qBittorrent, IP binding is set up, and it makes use of the kill switch function of the VPN. As a result, it is a better method than split tunneling to remain anonymous while downloading torrents.
5. Is IP binding necessary for using qBittorrent?
No. Although IP binding is optional, we strongly advise it as the best form of security.
You need to load content from reCAPTCHA to submit the form. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Turnstile. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Facebook. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou need to load content from reCAPTCHA to submit the form. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from reCAPTCHA. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Instagram. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from X. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information